Background & Problem
Imagine a bank losing every transaction record from the last 24 hours. Or a hospital unable to access patient records during an emergency. For enterprises, data loss isn't just an IT problem — it's a business crisis.
Data protection had no home in the platform
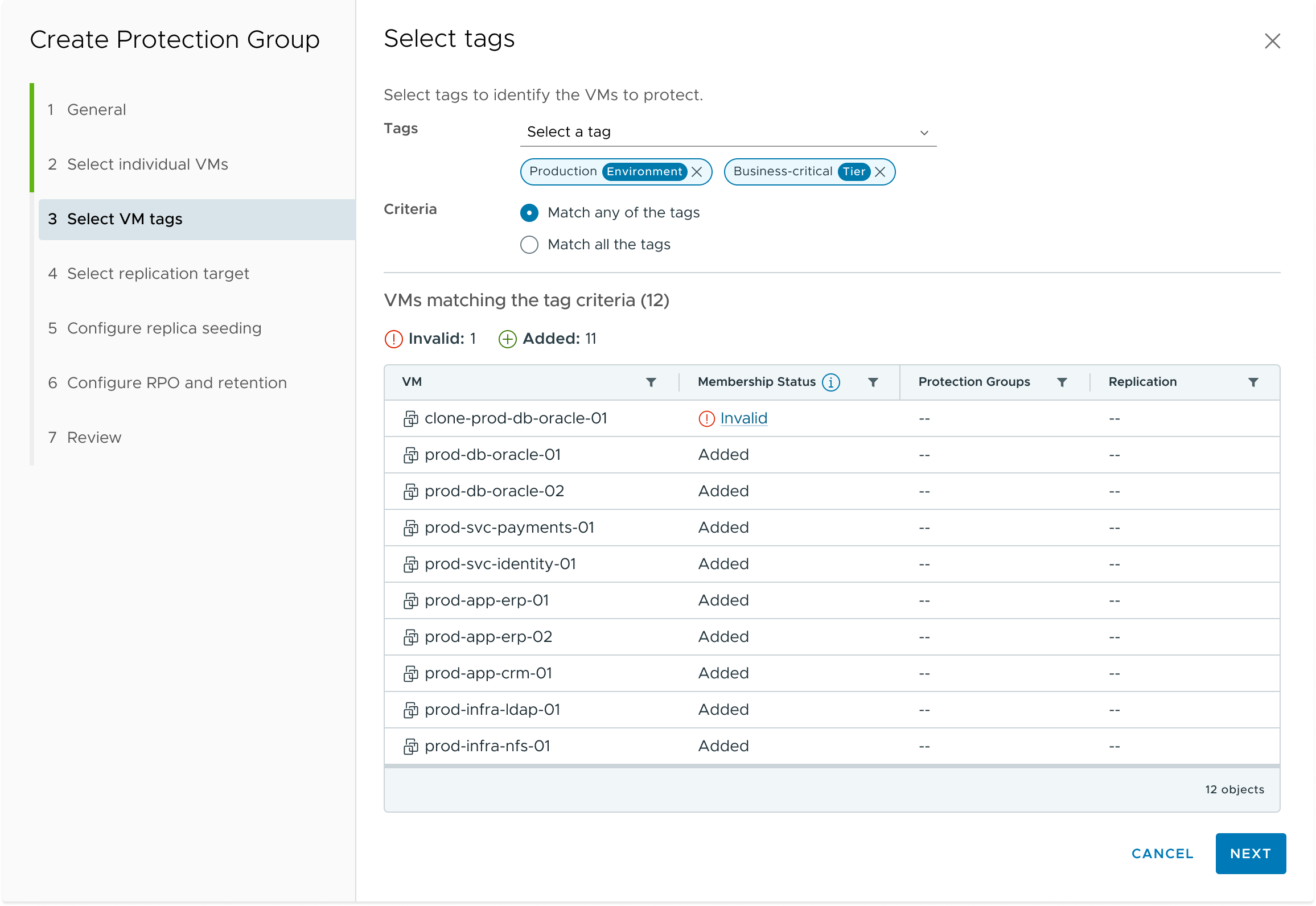
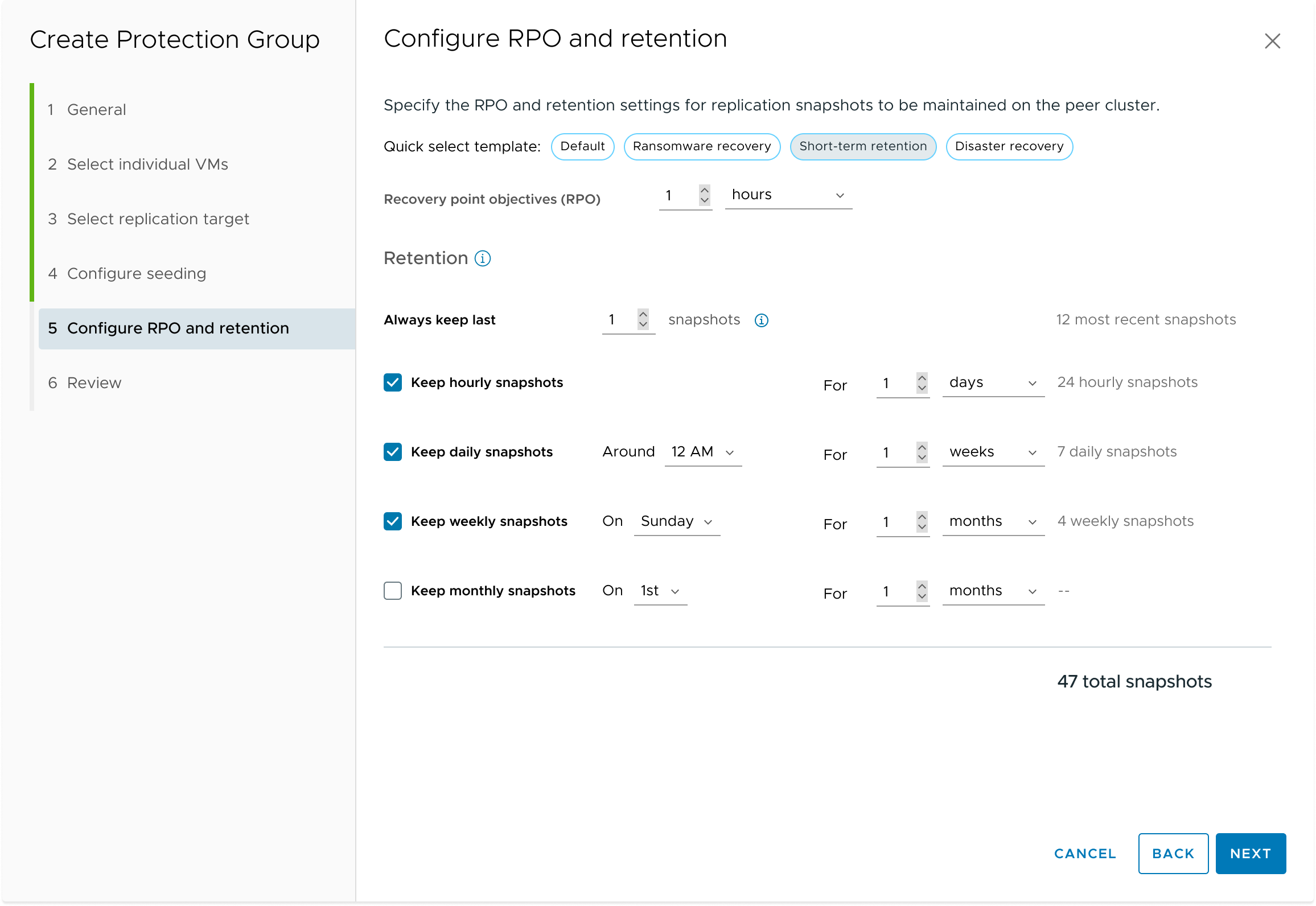
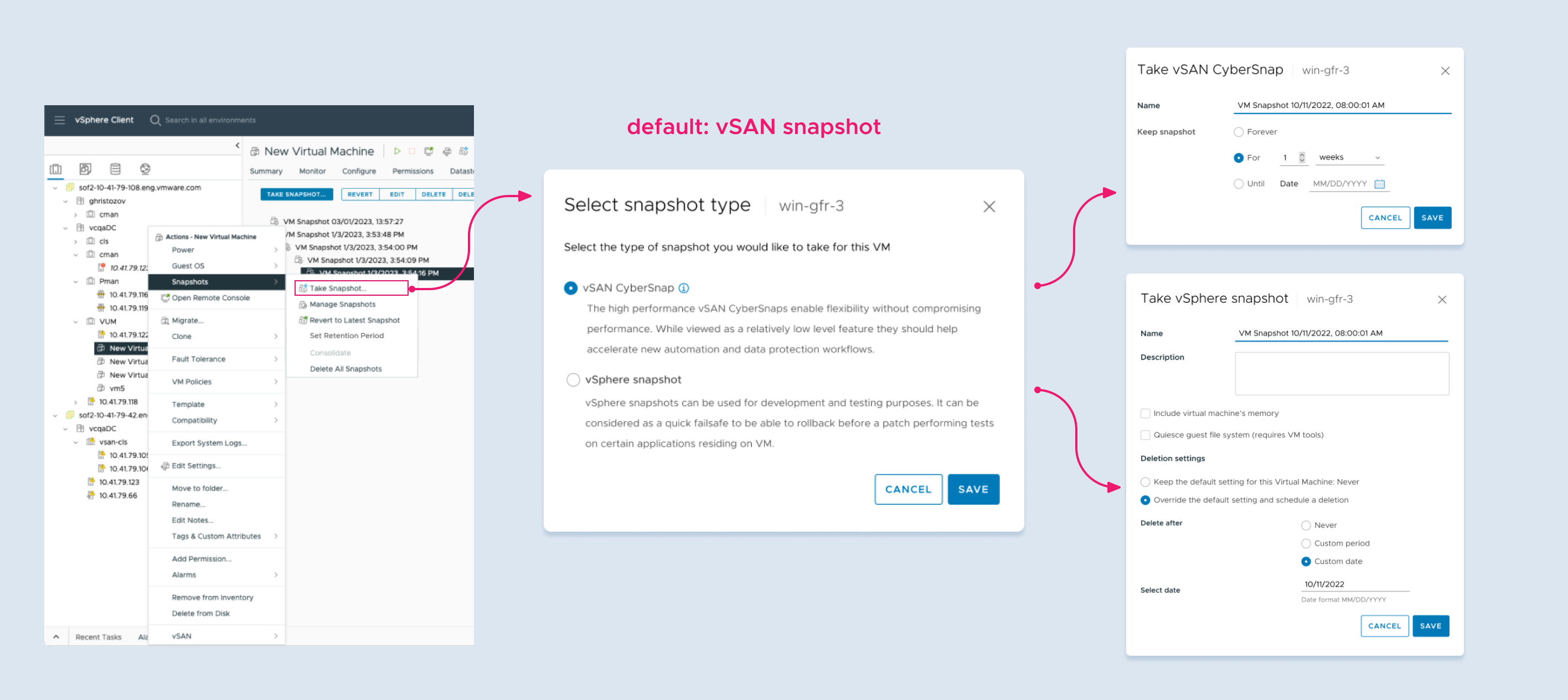
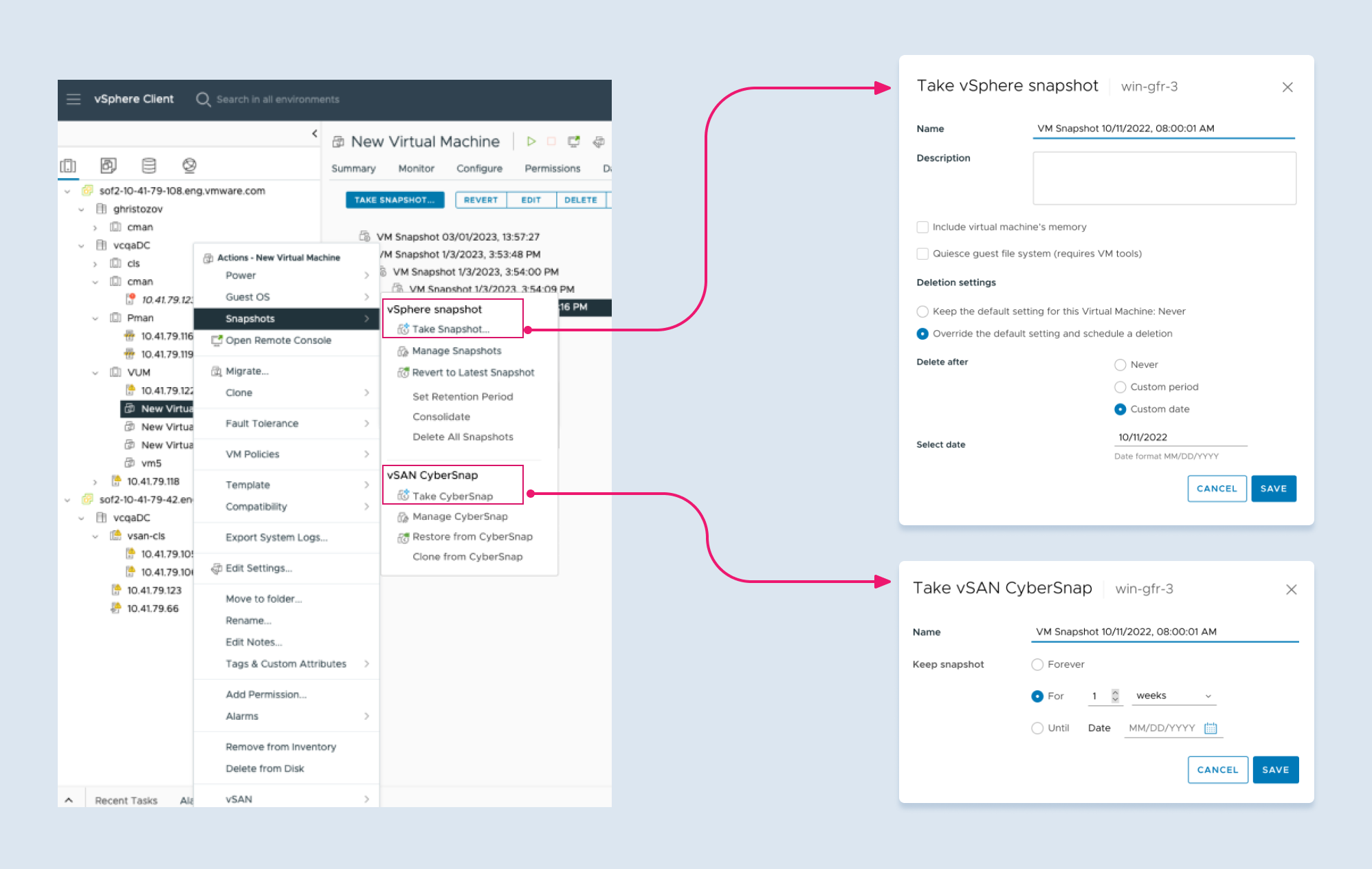
vSphere had a snapshot feature. It had no scheduling, no automation, and no retention policy. For enterprises with real compliance requirements, it wasn't enough.
Third-party tools — necessary, but costly
Infrastructure admins keep the lights on. Hundreds of VMs, storage, networking — across multiple datacenters, often with a small team.
Most teams filled the gap with third-party backup tools. That meant procurement, deployment, and integration work — before a single VM was actually protected.
 Infra Admin
Infra Admin
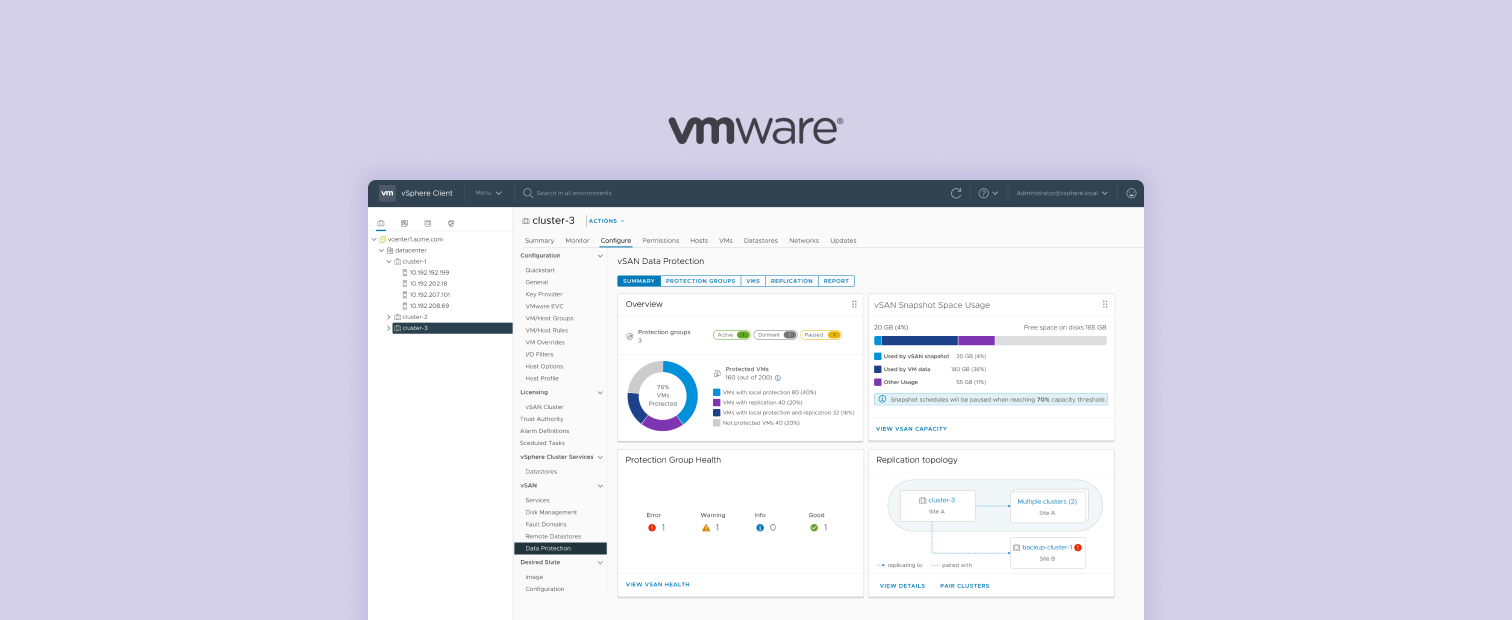
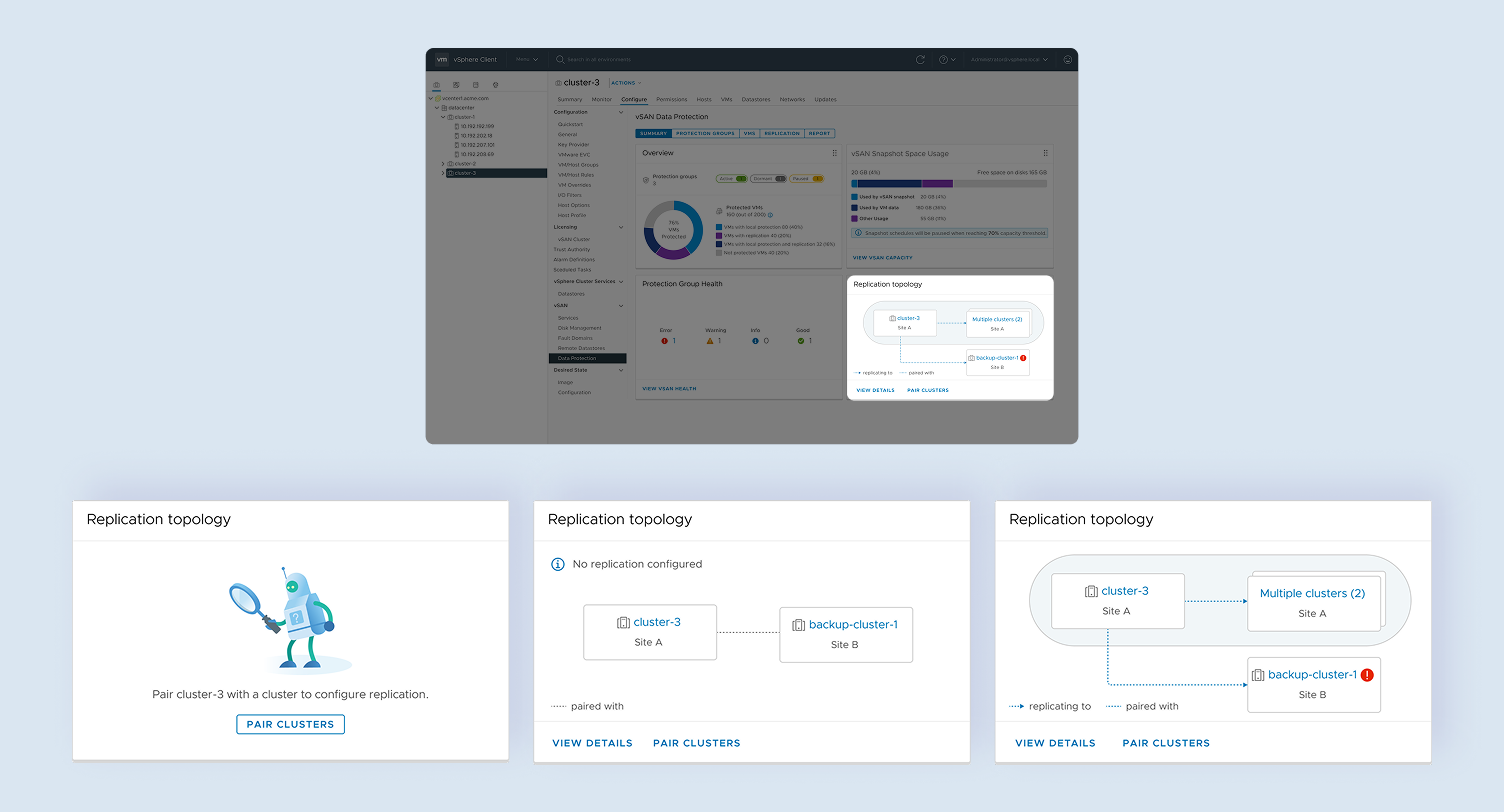
Build it natively — where admins already work
vSAN made native VM protection technically feasible for the first time. The opportunity: give infra admins data protection built into the tools they were already using — no separate product, no extra setup.